
In the digital age, data is a company’s most precious resource. If a business can protect its sensitive digital assets and data, it will have a clear advantage over competitors.
Cybersecurity training for employees helps organizations reduce the risk of cyber threats, and, in turn, prevents data breaches.
This blog will discuss how you can conduct cybersecurity training for your employees so that they possess the knowledge and skills required to protect your business’s confidential information.
But first, let’s understand why cybersecurity training is the need of the hour in the post-pandemic world.
Why Cybersecurity Training is Essential Post-Pandemic
An IBM report states that the global average cost for data breaches in 2021 stood at $4.24 million, which is a 9.8 percent increase from the previous year. On average, companies took 287 days to identify and contain data breaches; in 2022, it was 280.
The report further states that the US suffered the highest from data breaches.
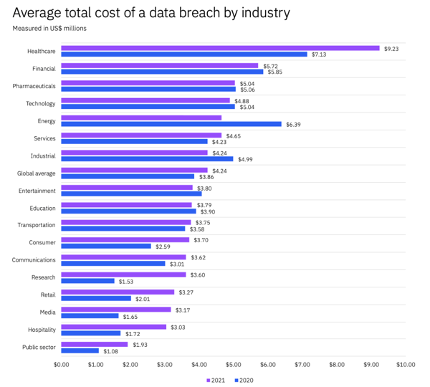
Image via IBM
The report clearly states that remote work was a significant factor in these growing data breach costs. Companies, where remote work was in place, suffered a $1.07m higher cost than those that didn’t have the remote working model.
Moreover, the rise of the work-from-anywhere model has led to more cybersecurity risks.
But, the good news is that companies can conduct cybersecurity training for their employees to teach them cybersecurity best practices.
Here is how you can conduct cybersecurity training for your employees.
How to Conduct Cybersecurity Training
Considering companies have a diversified workforce with different levels of technology expertise, here’s how you can conduct cybersecurity training within your organization.
1. Spread Awareness About Cybersecurity
The first step towards getting employees on board with cybersecurity training is to increase cybersecurity awareness among your employees. Hence, make sure that you educate your employees on the impact of data breaches and why cybersecurity is important.
Do note that the description should be comprehensible, relatable, and diverse:
- Comprehensible: Make sure your cybersecurity training message isn’t clouded by technical jargon that may confuse your employees. Use plain language whenever possible to reach non-tech-savvy individuals.
- Relatable: Cybersecurity is an external threat, so during the training, frame security as an issue of personal computer protection and home network intrusion. Employees will be able to relate more personally to the danger if it is described in terms of their phone, computer, or other forms of personalized data.
- Diversified: Employees may ignore a simple email message as they receive too many of them (thanks to email marketing automation). By diversifying your communications strategy, you can ensure that employees pay attention to the message rather than dismissing it as just another announcement.
2. Create Engaging Training Content
There is no replacement for engaging content in cybersecurity training materials. If they are dull, they will be minimized to a background browser tab.
But while a few jokes are nice to keep things light, it’s more important to address the employee’s perspective. Organizations should recount stories that connect cybersecurity issues to the business environment.
Keep it brief.
It’s much more likely that a five to seven-minute video will maintain the audience’s attention than a 45-minute lecture, no matter how well it is delivered.
A good idea is to make animated videos using vfx software to explain complicated cybersecurity concepts in an engaging manner. This can go a long way in helping your employees as you could share a copy of the video with them too for their reference.
3. Train Employees to Spot Suspicious Activities
Your cybersecurity training should empower the employees to become the first level of security.
You can teach them to keep their eye open for the following signs:
- System slowdown
- Loss of control over keyboard and mouse
- Sudden appearance of unwanted programs and software on the systems
- Strange pop-ups upon startup and before shutdown
- New tabs or extensions on the browsers
- Automatic files lost or copying
- Lucrative emails offering immediate money
You should encourage your employees to report any such suspicious activities instantly. It’s also important for your cybersecurity team to look at such things, even if they result in false alarms.
Arming your customer service team with these skills can be especially helpful if you’re selling a software product. They can use these service skills to help your customers avoid security breaches and could even help reduce the extent of damage with prompt actions.
4. Enforce a Zero-Trust Security Approach
The zero-trust security approach relies on the principle of ‘never trust, always verify’ to protect information.
Even if a device has been previously authenticated, it is treated as an untrusted device in a zero-trust security model. This makes it great for remote work as your employees could access your data from unsecured networks.
When you implement a zero-trust approach, make sure you share information about it with your employees so they get used to it.
5. Reinforce Confidentiality
When people work from home, they may become complacent about cybersecurity, and this is a problem.
Regardless of whether they are working from anywhere or from home, they still need to take passwords and authentication seriously. Cybersecurity threats loom large even if you’re working from home.
Hence, to protect your employees from data breaches, you should do the following in your security training:
- Encourage your employees to set unique passwords and change them periodically
- Explain why secure log-on processes, such as FastVPN and multi-factor authentication, are important, despite being time-consuming
- Provide examples of data theft caused by errant thumb drives or compromised personal Dropbox accounts to combat unsecured company data storage
You should request your remote employees to sign the confidentiality guidelines. To speed up the process, you can choose an eSign tool from the DocuSign alternatives.
6. Communicate Possible Cybersecurity Breach Examples
Your employees’ home network may not be as secure as an office environment with a controlled network. Some may connect via their home Wi-Fi, while others might utilize the public Wi-Fi at a café.
Moreover, some employees might use an older device that doesn’t support the latest security patches.
Hence, during cybersecurity training, employees must be encouraged to:
- Use devices that your company has provided. If you have a BYOD policy, check the device hardware and software for security patches.
- Do a security sweep of their home networks. For instance, some older routers may have weaker protocols like WEP, instead of WPA-2.
- Follow the set access control models by not sharing log-in credentials with other employees when accessing company data. These access models will prevent potential data breaches.
Also, develop a security policy for digital nomad employees, as roaming data or public Wi-Fi hotspots pose unique cybersecurity threats. And ask them to follow these appropriately.
Lastly, measure the results by conducting awareness surveys. You can use online form builders to create surveys and send them over to your employees regularly.
Wrapping Up
Training employees on cybersecurity is an attempt to foolproof the digital security infrastructure.
When every employee knows the right things to do to safeguard company data, cybercriminals will have the most difficult time getting through your network.



